[Federated] Security is no easy thing, let’s just state that out of the gate. That is why our Federated Security guru Dominick Baier has put together a two-day course. You can get some more details over here.
Posts, rants and any random thoughts about software development and technology in general.
Wednesday, December 21, 2011
Monday, December 19, 2011
Walk-through of provisioning Identity Server v1.0
Introduction
If you have the need to use your own Identity Provider, and want to go with something light (i.e.: not ADFS), Thinktecture’s Identity Server is your product. I have been using it for the last couple of months and I love it!! I actually added a service layer over it to enable my RP to provision users in the Identity Server (yes, I know that this is contrary to the general concept of outsourcing Identity Management, but in my scenario, trust me, it makes sense).From the CodePlex site:
Thinktecture IdentityServer is an open source security token service based on Microsoft .NET, ASP.NET MVC, WCF and WIF.
High level features
- Multiple protocols support (WS-Trust, WS-Federation, OAuth2, WRAP, JSNotify, HTTP GET)
- Multiple token support (SAML 1.1/2.0, SWT)
- Out of the box integration with ASP.NET membership, roles and profile
- Support for username/password and client certificates authentication
- Support for WS-Federation metadata
- Support for WS-Trust identity delegation
- Extensibility points to customize configuration and user management handling
Setup
Unzip the file and open the solution.
Because Identity Server (IdSvr) needs an ASP.NET membership database, we are going to set one up (if it doesn’t exist). There are some great tutorials on the web on how to do this (if you don’t already know), here is one of them.
After having installed the ASP.NET Membership database, we are going to update the connection string in IdSvr to point to said database.
The connection string file is located at \Configuration\connectionstring.config (Below is an example)
1: <connectionStrings>
2: <add name="ProviderDB"
3: connectionString="Persist Security Info=False;
4: User ID=sa;
5: password=****;
6: Initial Catalog=aspnetdb;
7: Data Source=mydbserver;"
8: providerName="System.Data.SqlClient" />
9:
>
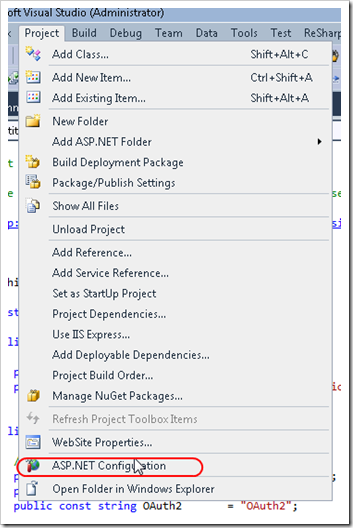
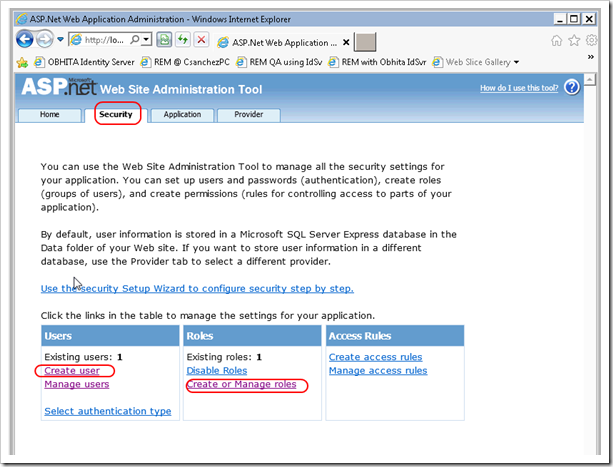
To test that the connection string works, in Solution Explorer, you should select the Website project, then from Visual Studio’s menu, select Project –> ASP.NET Configuration. This will launch the ASP.NET Web Site Administration Tool.

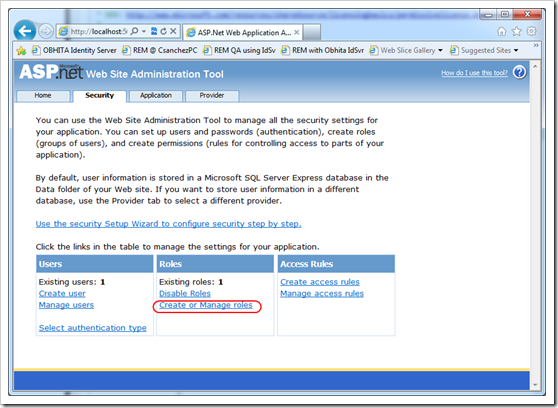
Using the ASP.NET Web Site Administration Tool, proceed to create a user (i.e.: Administrator) and a roles called IdentityServerAdministrators and IdentityServerUsers. These roles are important because they allow the user created to logon to IdSvr’s administration screen, and in the case of IdentityServerUsers, to be forwarded to the RPs upon successful login. These roles are specified in the Constants.cs file inside of the Thinktecture.IdentityServer.Core project.
1: public static class Constants
2: {
3: // ....
4: public static class Roles
5: {
6: public const string InternalRolesPrefix = "IdentityServer";
7: public const string Users = "Users";
8: public const string Administrators = "Administrators";
9:
10: public const string IdentityServerUsers = InternalRolesPrefix + Users;
11: public const string IdentityServerAdministrators = InternalRolesPrefix + Administrators;
12: }


Configuring IIS 7
Let’s proceed to configure IIS 7 to host the Identity Server website. We will need to:
- Request a Certificate for SSL (self-signed, Domain cert or commercial). Read this tutorial
- Setup https bindings. Go to this link, and scroll down to Create an SSL Binding.
Creating a certificate for Token Signing
The process of creating this certificate is the same as requesting a certificate for SSL. Why not just the SSL Certificate then? – May you ask?–, and the answer is:
“Using the SSL certificate for the token signing certificate will work – but this should not be the configuration you use in production. This is considered bad key hygiene.”
Source:Technet
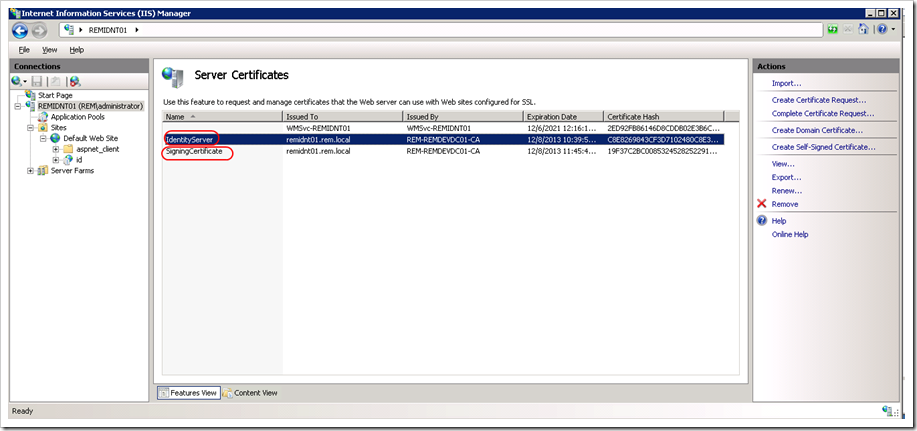
In my case, I have requested two certificates to the Domain Certificate Authority.
***UPDATE: Make sure the certificate Distinguished Name of each certificate is different (i.e.: Don’t request two certificates with the same attributes). I ran into an issue where IdentityServer’s x509Certificate Helper could not find the right certificate because there were two certificates, and it didn’t like that.
var certs = store.Certificates.Find(findType, value, false); if (certs.Count != 1) { throw new InvalidOperationException(String.Format("Certificate not found: {0}", value)); }
We are almost there.
Configuring Identity Server
You should be able to navigate to Identity Server’s URL. If the certificates you created are not trusted by your computer, you see this screen. This occurs if you are using a certificate issued by a CA your computer does not trust. Here is a link on how to trust the certificate.

You should be seeing Identity Server’s initial configuration screen. Go ahead and customize the first two fields to match your environment, and select the certificate that will be used for token signing.
UPDATE: Make sure that the IIS Worker Process Identity has access to the Private Key of your certificates. Use the Certificate MMC for this.

Tada!! You have successfully configured Identity Server and should be ready to add your application as a Relaying Party (RP). You can find a tutorial on how to do that over here (scroll down to 2.Register an existing production STS).

Sunday, November 13, 2011
CMAP CodeCamp Slide Deck
I have started the process of going from having a wealth of opinion and a lack of experience, to a more balanced mix. I have made a mental note of a myriad of things that need to be improved, and will continue to improve the talk and gain more experience every time I do it.
Thanks to the audience for being so patient with me and not have walked out on me. The slides are here.
Wednesday, September 28, 2011
Setting up Thinktecture’s Identity Server
The following tutorial assumes the reader is familiar with the following technologies/concepts:
- Single Sign-on (SSO)
- Windows Identity Foundation (WIF)
- Active Directory Federation Services
- Claims-based identity
This post is a how to setup Thinktecture’s StarterSTS Identity Server [B1].
1. Download the Source Code from the Codeplex site [at the time of this writing, the current version is B1 Refresh] and unzip it on your local drive.
2) Once the Solution is opened in Visual Studio, inside of the Tools solution folder you will find a Setup project. Run the project by right clicking on it, Selecting Debug –> Start new instance.
3) Set the Location of the Configuration Database as shown below.
You can find the file called IdentityServerConfiguration.sdf inside of the App_Data folder of the Website Project.
4) Select the certificate that will be used for SSL Encryption. **Note: If you already have IIS setup with SSL, you most definitely want to use the same certificate. I suspect you will, because if you are installing this Identity Server you must be very familiar with the Windows Identity Foundation configuration dance.
5) Select the certificate that will be used for Signing (You can use the same certificate)
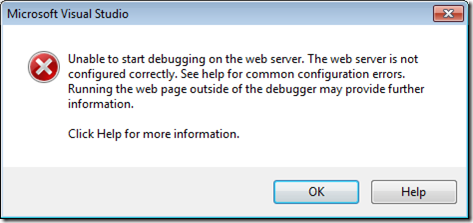
After this is done, you might be thinking that you can run the [website] project now and it should just work, right? Thought WRONG! There is no free meal in this world. Our friend Dominick [Baier] has had this running on his machine for a while, so perhaps forgot about setting up IIS, the ASP.NET provider Database and all that business.
SEtting up ThE WEBSITE PROJECT TO USE IIS
So, right after you download the source code, the Web Project Properties looks like so:
Notice the “[X] Use Custom Web Server” option is selected, and points to https://roadie/idsrv/. You want to change these setting as follows:
Switch the setting to Use Local IIS Web Server and enter a more appropriate URL (i.e.:http://[your machine’s fully qualified name]/idsrv), or if you are one cool cat, you may choose Use IIS Express (but then, you are on your own).
We are almost there, do not despair.
CONFIGURING THE ASP.NET MEMBERSHIP DB.
If you were to try to run the Website, you should get this “Yellow page of death”. And that is due to the fact (if you are one of those who do no read error pages) that the 1) you have not installed the standard ASP.NET Membership schema, and 2) the Identity under which IIS is running does not have access to said database (provided it existed). Follow these instructions to setup the ASP.NET application services schema.
After having installed the ASP.NET Schema on your SQL Server instance, go to SQL Server Management Studio, and under Security –> Logins, and make sure that the Identity under which your IIS Application Pool is running has a valid login in SQL Server and has the right access to the ASP.NET database. In my case, the App pool Identity is 'IIS APPPOOL\DefaultAppPool' and the database named "aspnetdb".
Lastly, change the Website\Configuration\connectionStrings.config file to point to your ASP.NET application services database.
<connectionStrings><add name="ProviderDB"connectionString="data source=.\sqlexpress;Integrated Security=SSPI;Initial Catalog=aspnetdb"providerName="System.Data.SqlClient" /><add name="IdentityServerConfigurationEntities"connectionString="metadata=res://Thinktecture.IdentityServer.Core/Repositories.SqlCompact.IdentityServerConfiguration.csdl|res://Thinktecture.IdentityServer.Core/Repositories.SqlCompact.IdentityServerConfiguration.ssdl|res://Thinktecture.IdentityServer.Core/Repositories.SqlCompact.IdentityServerConfiguration.msl;provider=System.Data.SqlServerCe.4.0;provider connection string="Data Source=|DataDirectory|\IdentityServerConfiguration.sdf""providerName="System.Data.EntityClient" /></connectionStrings>
If you did everything right, you should now be able to run the application and get this page.
Accessing the Administration Mode of Identity Server
Out of the box, IdentityServer is configured to use the SqlMembershipProvider membership provider implementation. Therefore to login you have to:
- create a user (i.e.: Administrator)
- create a role called IdentityServerAdministrators.
Both of these can be accomplished by using the built-in Web Site Administration Tool (in Visual Studio, go to Project –> ASP.NET Configuration).
[FYI] Contrary to what Dominik Baier’s introductory video says [9:02] , the role the code is expecting is not “TokenServiceAdministrators”, but instead, IdentityServerAdministrators).
[Change for Improvement] This can be improved in the future by modifying the provided implementation of ClaimsAuthorizationManager, and changing the AuthorizeAdministration Method (inside of Thinktecture.IdentityServer.Web.Security.AuthorizationManager)
protected virtual bool AuthorizeAdministration(Collection<Claim> resource, IClaimsIdentity id){return (id.ClaimExists(ClaimTypes.Role, Constants.Roles.IdentityServerAdministrators));}
The next article will describe how to create a configure your application (Relaying Party) to trust Identity Server as an Secure Token Service (STS).